This article shows how to force phishing resistant authentication for external B2B users using a cross tenant trust. The external users are from a separate tenant and the local tenant needs to trust the multiple factor authentication (MFA) from the other known tenants. This prevents the user having to authenticate again and setup more MFA.
Code: https://github.com/damienbod/AspNetCoreAzureADCAE/tree/main/RazorCaePhishingResistant
The demo application requires that administrators use a phishing resistant MFA and this is implemented using an Azure AD authentication context with a policy. The tenant and the application was setup as shown in the blog:
Force phishing resistant authentication in an ASP.NET Core application using Azure AD
If a local member authenticates using a phishing resistant MFA, the user can access the admin page without problem.
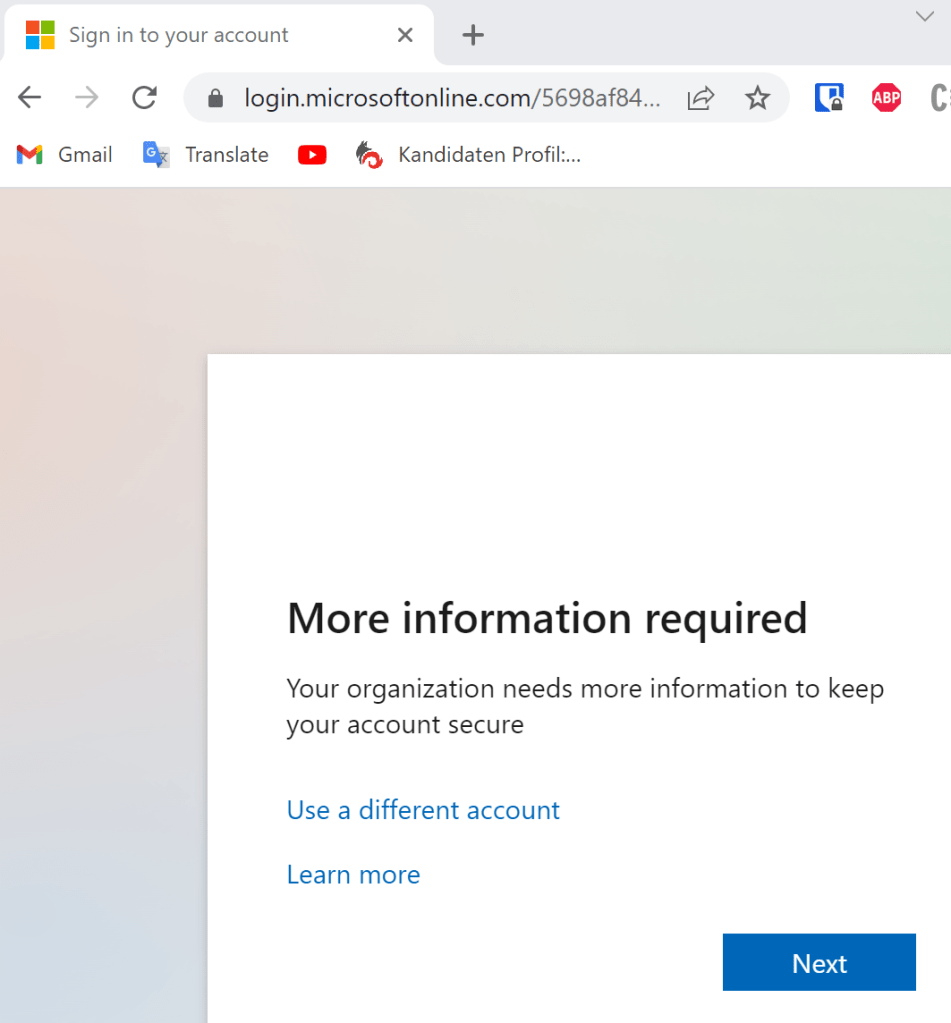
When an external member or a guest user authenticates, the user will be shown the following page requesting that the user authenticates again with a correct MFA. This is displayed even if the user has authenticated correctly on the home tenant. No trust exists between the Azure AD tenants.
To fix this, the Azure tenant must trust the multiple factor authentication from the other tenants. This can be implemented using Azure AD external identities.

Now when the user authenticates, everything will work.
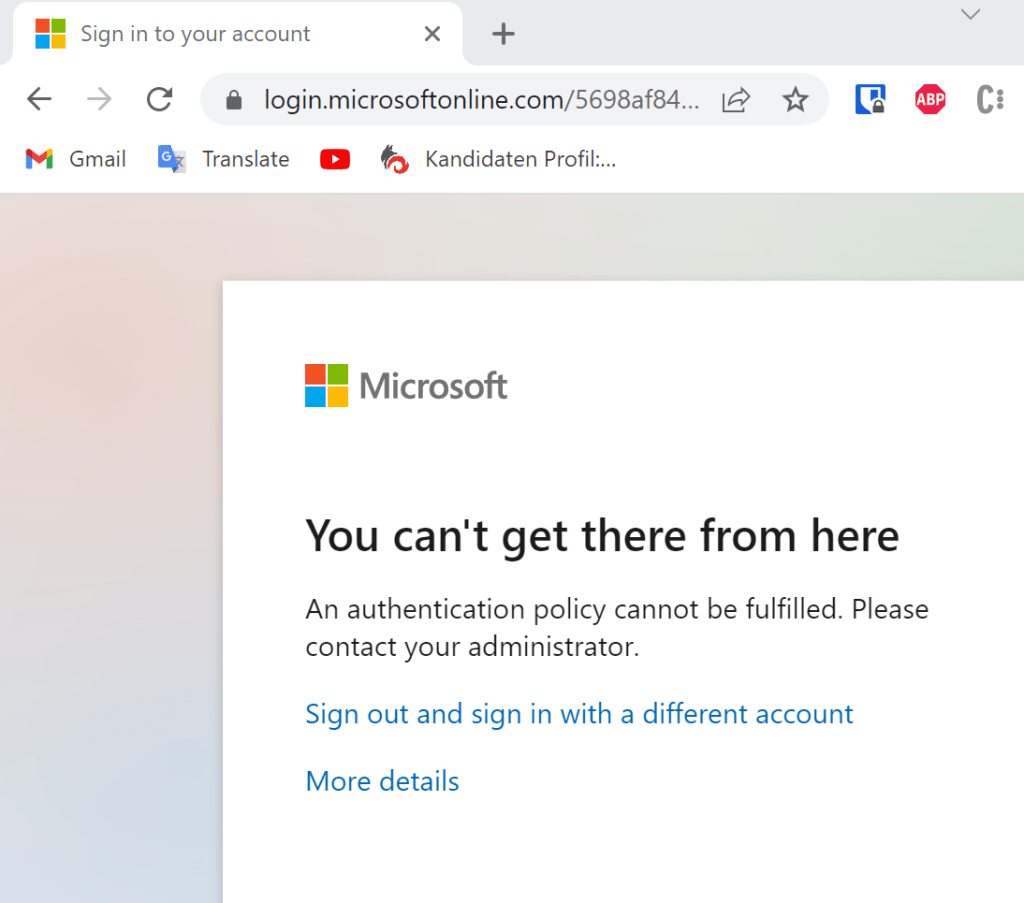
One problem which still exists is for Microsoft accounts. These users cannot authenticate with the step up requirement.
Links
https://learn.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-mfasettings

[…] Trust phishing resistant MFA for cross tenant users [#.NET Core #ASP.NET Core #OAuth2 #Security #Web #aspnetcore #Azure #CAE #dotnet] […]
[…] Trust phishing resistant MFA for cross tenant users (Damien Bowden) […]
[…] Trust phishing resistant MFA for cross tenant users – Damien Bowden […]