This article shows how to implement Azure Privileged Identity Management access in an ASP.NET Core application using an Azure security group. An Azure Conditional Access Authentication context is used for the Azure administrator giving access to the group for Azure AD users. The Authentication context is setup to require a phishing resistant authentication. An Enterprise application is used to only allow assigned members of the security group access to the ASP.NET Core application. The application can only be used as specified in the Azure PIM member definition.
Code: https://github.com/damienbod/AzurePim
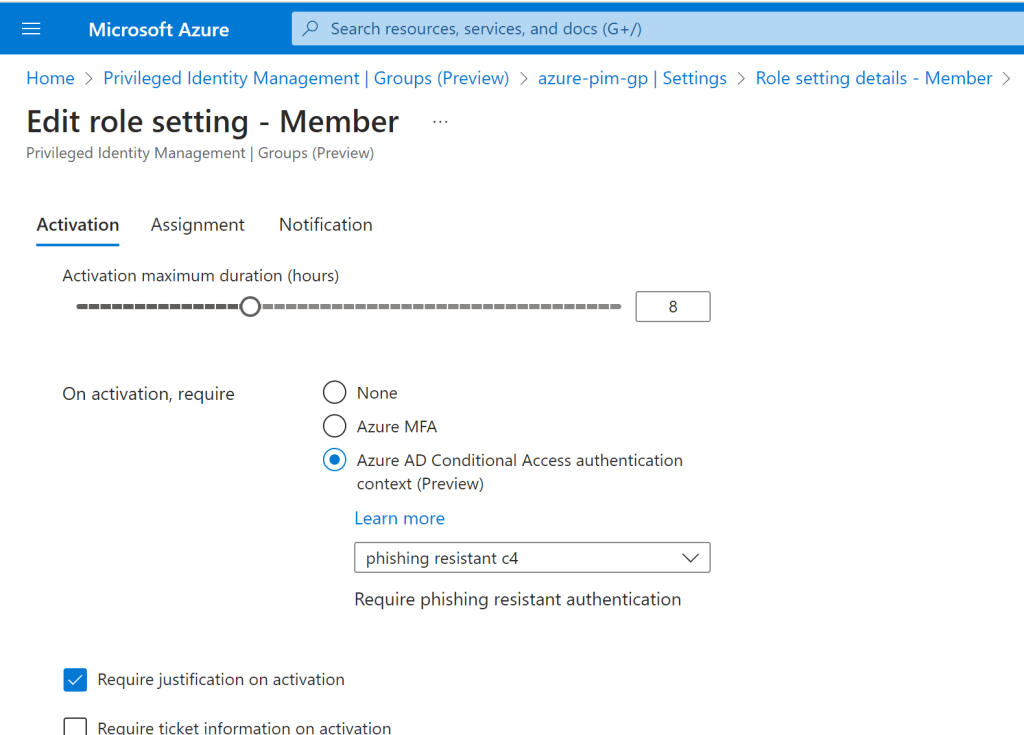
A Conditional Access Authentication context is setup so it can be used in the PIM group configuration. This Authentication context is used in an Azure CA policy which requires a phishing resistant authentication.

An Azure security group was created and this group was onboarded to the PIM groups definitions. The Azure Authentication context is used for activation. The administrator activating users in this group must have authenticated using a phishing resistant authentication.
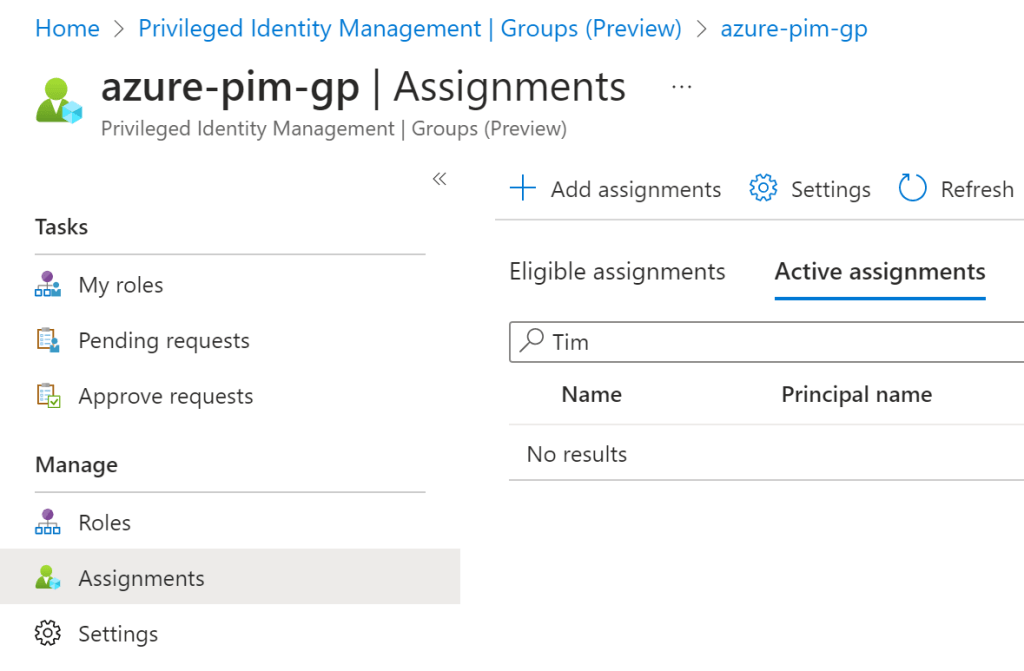
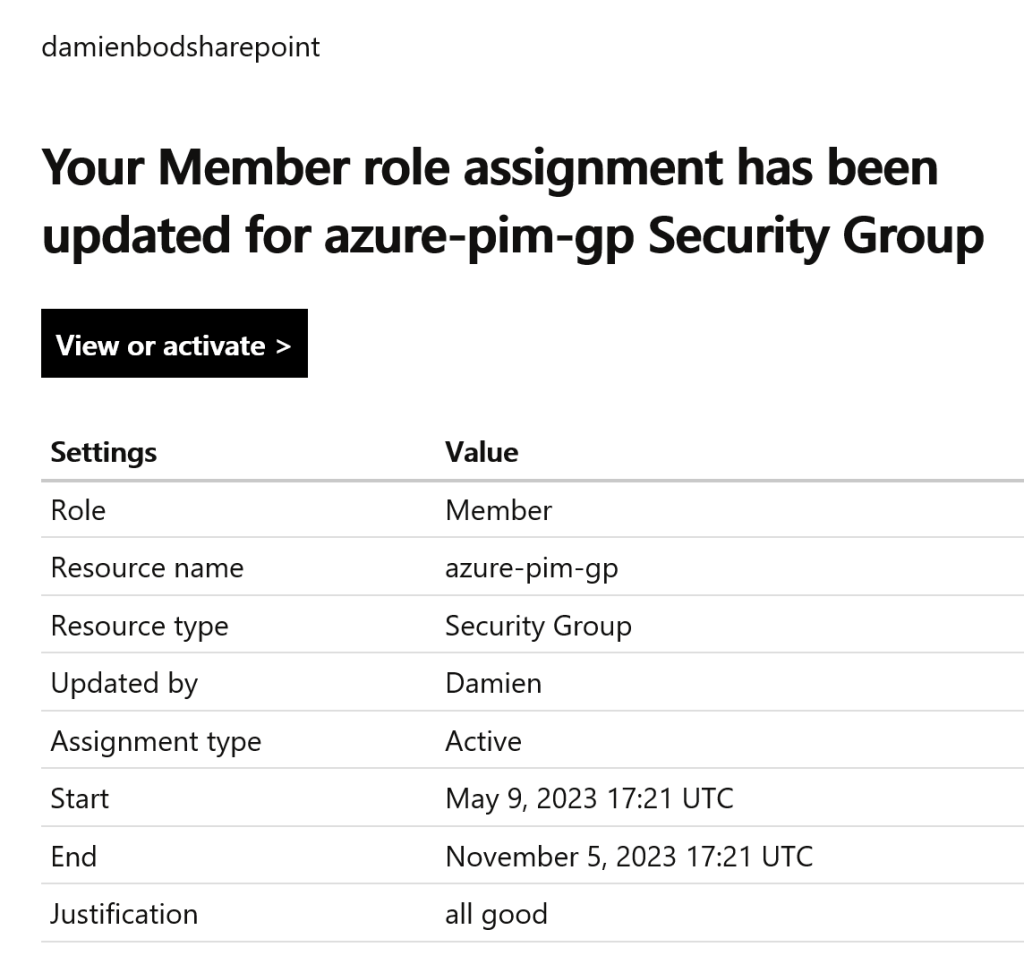
User assignments can be added to the group. Each assignment requires a reason description which is sent in the email notification.
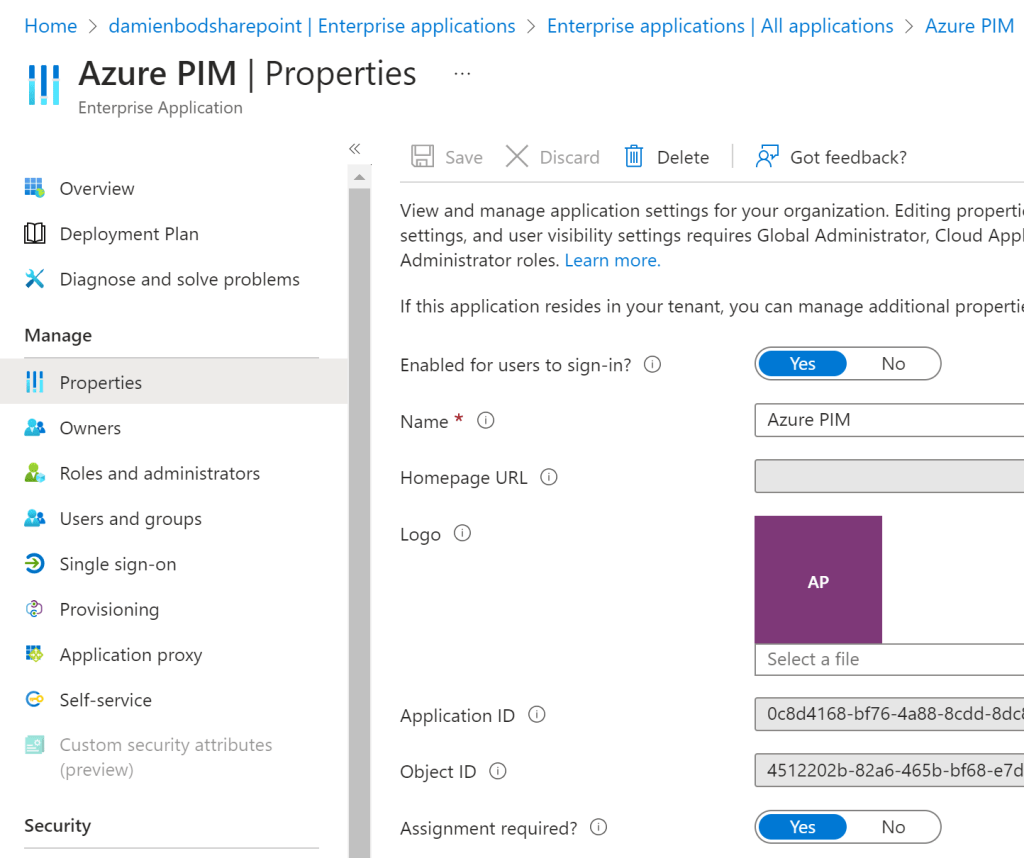
The Enterprise application used for the ASP.NET Core application is setup to only allow assigned users from the Azure security group. The Assignment Required is set to true.
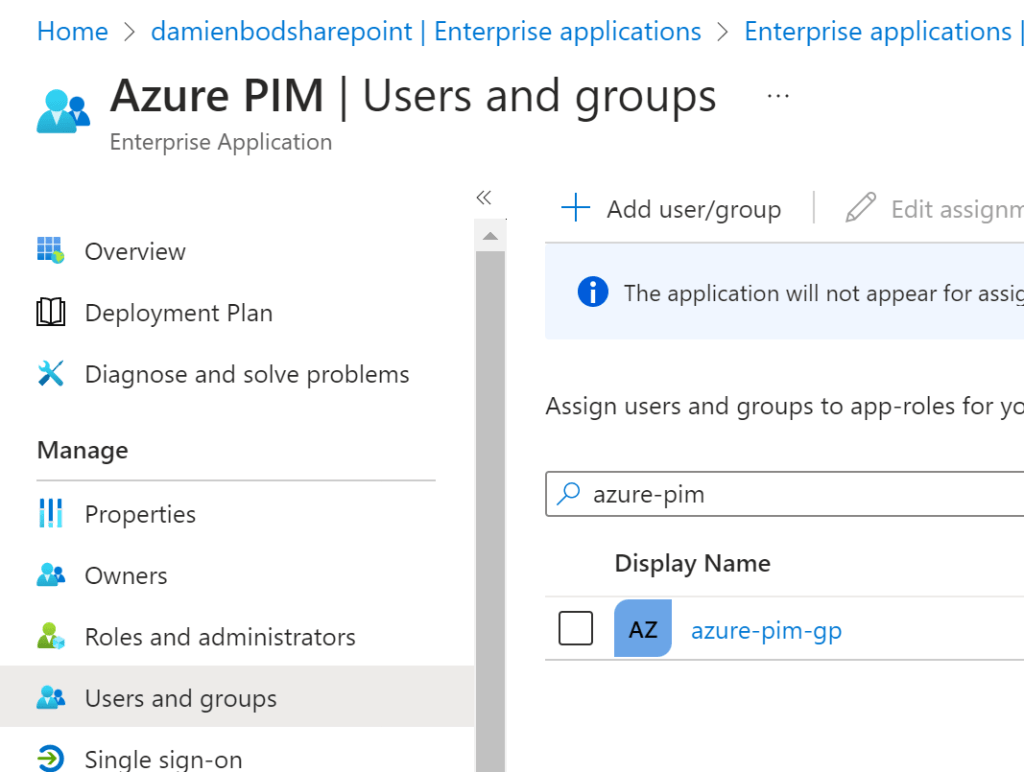
In the users and the groups, the security group is added.
The ASP.NET Cor application is created to authenticate using the Azure App registration with a secret, meaning the application is a confidential client. Public applications should not be used for administration business processes. Microsoft.Identity.Web is used to implement the confidential OpenID Connect client using the code flow and PKCE.
builder.Services.AddAuthentication(
OpenIdConnectDefaults.AuthenticationScheme)
.AddMicrosoftIdentityWebApp(
builder.Configuration.GetSection("AzureAd"))
.EnableTokenAcquisitionToCallDownstreamApi()
.AddDistributedTokenCaches();
builder.Services.AddRazorPages()
.AddMicrosoftIdentityUI();
When a user is assigned, an email is sent to the user and the user can use the application to authenticate and gain access to the application.
Notes
A lot of the different features from the Azure AD access management was used in the setup. You could also force all users in this group to use a phishing resistant policy by applying the same authentication context to the group and not just the PIM administrator assigning users to the group. You could also use roles instead of groups in the PIM. There are lots of different possibilities and it is imported to choose the correct ones for your environment following KISS. If you don’t need it, then don’t use it. PIM requires an Azure P2 license. Azure AD PIM + Conditional Access integration can be used to force all types of business security requirements and features.

[…] Use Azure PIM with groups in ASP.NET Core [#.NET #.NET Core #ASP.NET Core #Azure #Azure AD #aad #AzureAD #groups #PIM #security groups] […]
[…] Use Azure PIM with groups in ASP.NET Core (Damien Bowden) […]
[…] Use Azure PIM with groups in ASP.NET Core – Damien Bowden […]