This article shows how to implement FIDO2 passwordless authentication with Azure AD for users in an Azure tenant. FIDO2 provides one of the best user authentication methods and is a more secure authentication compared with other account authentication implementations such authenticator apps, SMS, email, password alone or SSI authentication. FIDO2 authentication protects against phishing.
To role out the FIDO2 authenitcation in Azure AD and setup up an account, I used the Feitian FIDO2 BioPass K26 and K43 security keys. By using biometric security keys, you get an extra factor which is more secure than a pin. The biometric data never leaves the key. You should never share any biometric data anywhere or share on any shared server.
I used the Feitian BioPass FIDO2 Manager to setup my security keys using my fingerprint. This is really easy to use and very user friendly.

Setting up the Azure AD tenant
The FIDO2 security key authentication method should be activated on the Azure AD tenant. Disable all other authentication methods unless required. Also disable SMS authentication, this should not be used anymore. All users should be required to use MFA.

Now that the Azure AD tenant can use FIDO2 authentication, an account can be setup for this. If you implement this for a company’s tenant, you would role this out using scripts and automate the process. You can sign in to your account at Microsofts myaccount website and use the security info menu to configure the Feitian FIDO2 keys.
https://myaccount.microsoft.com/
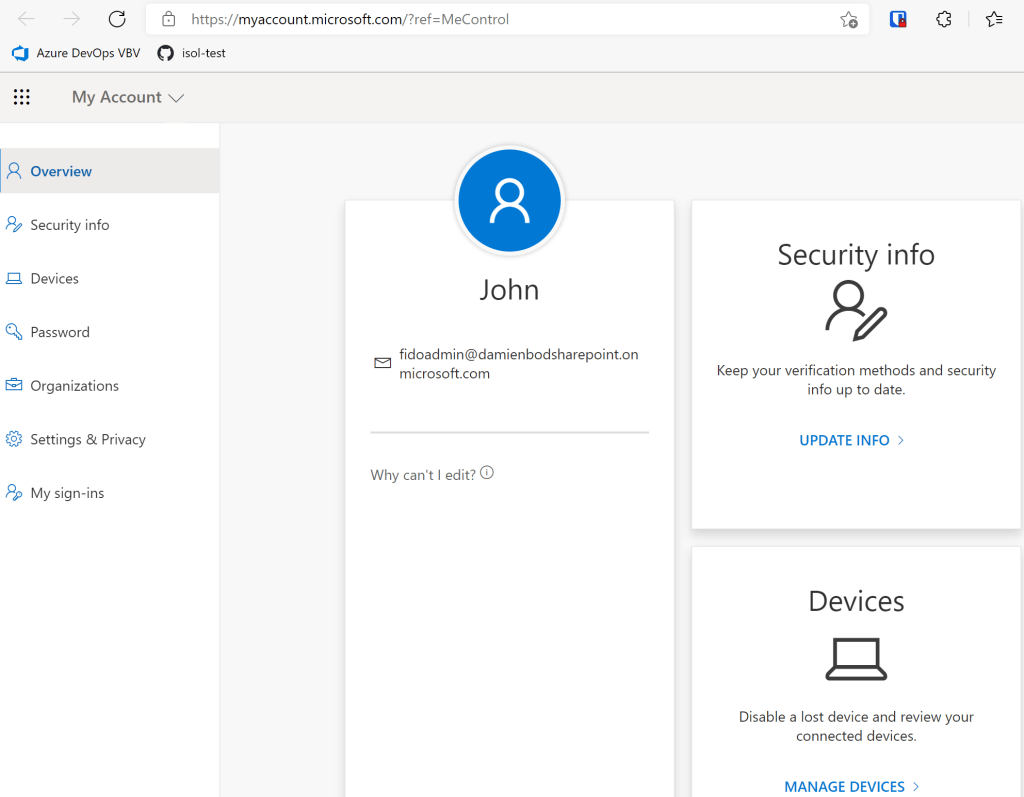
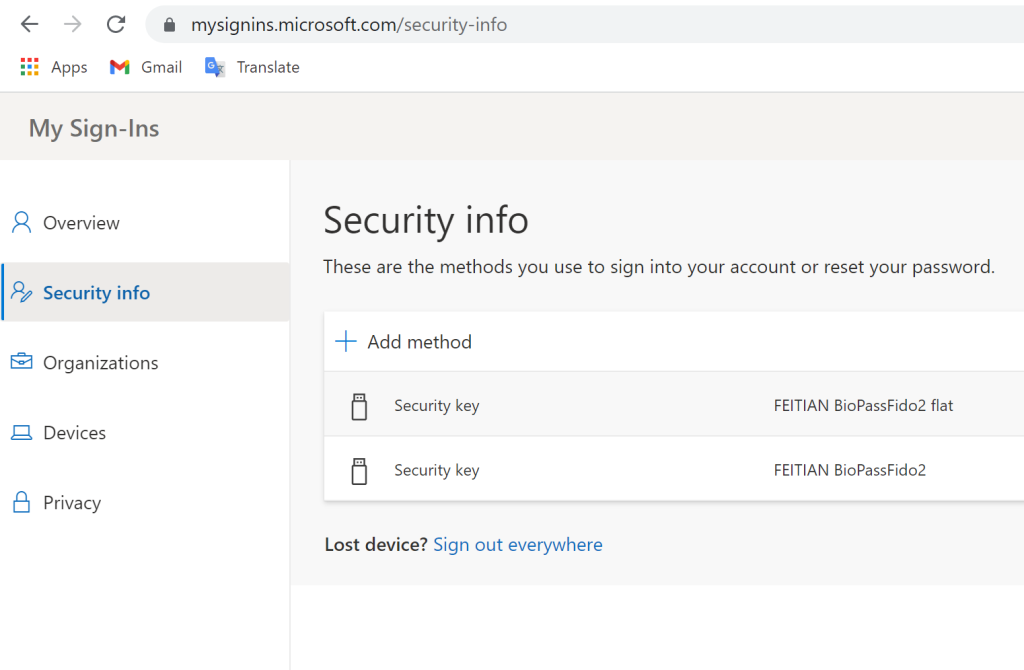
I added my two security keys using USB. I use at least two security keys for each account. You should use a FIDO2 key as a fallback for the first key. Do not use SMS fallback or some type of email, password recovery. Worst case, your IT admin can reset the account for you and issue you new FIDO2 keys.
https://mysignins.microsoft.com/security-info
Using FIDO2 keys with Azure AD is really easy to setup and works great. I use FIDO2 everywhere which supports this and avoid other authentication methods. Some of the account popups for Azure AD is annoying trying to authenticate using password, SMS or email, I would prefer FIDO2 first for a better user experience. The Feitian BioPass FIDO2 security keys are excellent and I would recommend these.
Links:
https://www.microsoft.com/en-us/p/biopass-fido2-manager/9p2zjpwk3pxw
https://myaccount.microsoft.com/
https://mysignins.microsoft.com/security-info
https://www.ftsafe.com/article/619.html
Configure a FEITIAN FIDO2 BioPass security key
https://www.w3.org/TR/webauthn/

[…] Use FIDO2 passwordless authentication with Azure AD [#Azure #Azure AD #2FA #aad #AzureAD #Feitian #Fido2 #MFA #passwordless] […]
[…] Use FIDO2 passwordless authentication with Azure AD (Damien Bowden) […]
[…] Use FIDO2 passwordless authentication with Azure AD – Damien Bowden […]