This article looks at the authentication pyramid for signing into different applications. I only compare flows which have user interaction and only compare the 2FA, MFA differences. A lot of incorrect and aggressive marketing from large companies are blurring out the differences so that they can sell their products and so on.
When you as a user need to use an application, you need to login. The process of logging in or signing in requires authentication of the user and the application. The sign in or login is an authentication process.
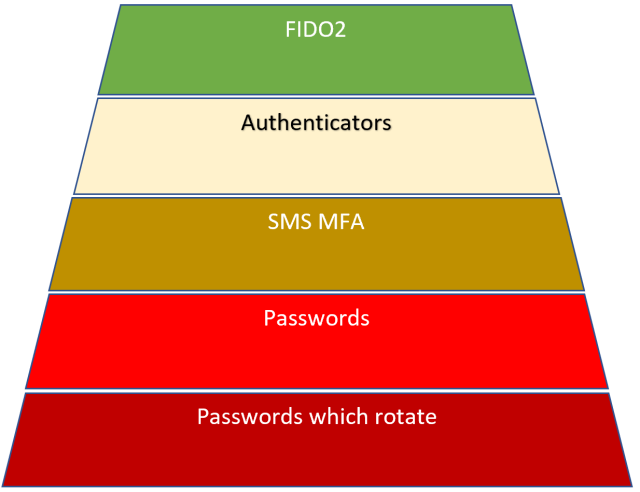
To explain the different user and application (identity) authentication possibilities, I created an authentication pyramid diagram from worse to best. FIDO2 is the best way of authenticating as this is only one which protects against phishing.
Passwords which rotate
Passwords which rotate without a second factor is the worst way of authenticating your users. By forcing password rotation, people are forced to update passwords regularly and this discourages the use of password managers and encourages users to use something simple which they can remember. In companies which use this policy, a lot of users have a simple password with a two-digit number at the end of the password. You can guess the number by calculating the length of time the user was at the company and the amount of time a password is active.
Passwords
Passwords without a second factor which don’t rotate are better than password which rotate as people tend to use better passwords. It is easier to educate the organisation users to use a password manager and then any complicated password can be easily used without constant rotation, annoyance. If it’s a pain to use in your daily routine, then people will try to avoid using it. I encourage users to use bitwarden but most password managers work good. Ease of use in the browser is important.
SMS MFA
SMS as a second factor is way better than passwords alone. But SMS as a second factor has too many security problems and is too easy to bypass. NIST no longer recommends using SMS as a second factor.
https://pages.nist.gov/800-63-3/sp800-63b.html
Authenticators
Authenticators are a good solution for second factor authentication and does improve the quality and the security of the authentication process compared to passwords and SMS second factor. Authenticators do have many problems, but the major fault of authenticators is that it does NOT protect against phishing. When using authenticators, your users are still vulnerable to phishing attacks.
If a user accesses a phishing website, the push notification will still get sent to the mobile device or the OTP can still be validated. A lot of companies are now moving to 2FA using authenticators. One problem with this is that the push notifications seems to get sent randomly from Authenticators. Authenticators are NOT enough if you have high security requirements.
Most people will recognise the popup underneath. This popup opens on one of my domains on almost a daily basis. I see users conditioned now to just click the checkbox, give in the code and continue working without even checking which application requested this. It has become routine now to just fill this in and click it away so that you can continue working. Sometimes the popup just opens because the last code has timed out. If someone had acquired your password and was logging in, a few users would just enter the code for the attacker due to this conditioning. Also, if you were accessing your application through a phishing website, you would not notice any difference here and continue to validate with the code.

Another problem with authenticators is that it requires a mobile phone to install the application. To complete the login, you require a phone. Most of us only have one mobile phone, so if you lose your phone, then you are locked out of your accounts. The account recovery comes into play which is usually a password, or SMS. Your security is reduced to SMS or password if you use this type of recovery. If recovery requires your IT admin to reset the account, you must wait for the IT from your organisation to reset your account, but this way, the security stays at the authenticator security level.
It is important that the account recovery does not use a reduced authentication process.
FIDO2 (Fast IDentity Online)
FIDO2 is the best way to authenticate identities where user interaction is required. FIDO2 protects against phishing. This is the standout feature which none of the other authentication processes protect against. If you lose your FIDO2 key, then you can use a second FIDO2 key. You as an organisation no longer need to worry about phishing. This could change in the future, but at present FIDO2 protects against phishing.
If you are an organisation with 100 employees, you could only allow FIDO2 and block all other authentication methods. Each employee would require 2 FIDO2 keys which would cost roughly 100$. This would cost about 10k for 100 users and so fully protect an organisation and rid yourself from phishing. You could save all the costs of the phishing exercises which so my companies force us to do now.
Here’s how you could configure this in Azure AD using the security, Authentication methods:

Notes:
Passwordless is great when using FIDO2. FIDO2 has best practice and recommendations for which FIDO2 flow, when and where to use. There are different type of FIDO2 flows for different use cases.
Passwordless is not only FIDO2, so be careful implementing a Passwordless flow. Make sure it’s a FIDO2 solution.
If you are using FIDO2, you will require NFC on the mobile phones to use applications from the organisation, unless you allow FIDO2 hardware from the device.
Identity authentication is only one part of the authentication. If you use a weak OAuth2/OIDC (OpenID Connect) flow, or something created by yourself, you also can have a weak authentication even if using FIDO2. It is important to follow standards. For example using FIDO2 authentication with OIDC FAPI would give you a really good authentication solution.
Try to avoid non-transparent solutions. Big companies will always push their own solutions and if these are not built using standards, there is no way of knowing how good the solution is. Security for your users is not the focus for the companies selling security solutions, selling their SOLUTION is the focus. It is up to you to know what you are buying. Security requires a good solution for application security and network security. A good solution will give you the chance to use best practice in both.
I would consider OIDC FAPI state of the art for high security in applications. This is what I would now consider when evaluating solutions for banks, insurance or government E-Ids. Using this together with FIDO2 and you have an easy to use best practice security solution.
Links
https://pages.nist.gov/800-63-3/sp800-63b.html
https://portal.azure.com/#blade/Microsoft_AAD_IAM/AuthenticationMethodsMenuBlade/AdminAuthMethods
https://docs.microsoft.com/en-us/aspnet/core/security/authentication/mfa
https://fidoalliance.org/fido2/

[…] The authentication pyramid – Damien Bowden […]
[…] The authentication pyramid […]
[…] The authentication pyramid […]
[…] The authentication pyramid […]
[…] The authentication pyramid […]
[…] The authentication pyramid Posted in News […]
[…] The authentication pyramid Implement ASP.NET Core OpenID Connect with Keycloak to implement Level of Authentication (LoA) requirements […]