This article shows how to create an Azure Resource Manager (ARM) template which uses an Azure Key Vault. The ARM template is used to deploy an ASP.NET Core application as an Azure App Service. By using an Azure Resource Group project, the secret app settings can be fetched from the Azure Key Vault during deployment, and deployed to the Azure App Service. This makes it easy to automate the whole deployment process, and no secrets are added to the source.
Different services can then use the same secrets from the Azure Key Vault, so it is easy to change the secrets regularly. The Key Vault is only used during deployment.
A problem with this approach is that if secrets are shared across services, then all services need to be updated at the same time when the secret is changed. If the services were using the secrets directly, then the secret could be updated directly, although the services would have to use the new value, which usually means an application restart.
Code: https://github.com/damienbod/AspNetCoreBackChannelLogout
Posts in this series:
- OpenID Connect back-channel logout using Azure Redis Cache and IdentityServer4
- Using Azure Key Vault with ASP.NET Core and Azure App Services
- Deploying ASP.NET Core App Services using Azure Key Vault and Azure Resource Manager templates
- Using Azure Key Vault from a non-Azure App
Create an Azure Resource Group project
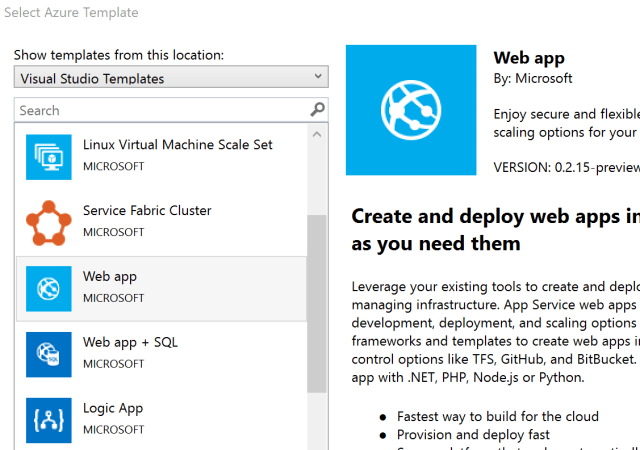
In Visual Studio, click the Cloud menu, and select a “Azure Resource Group” type.

Then choose a Web APP as the target project will be deployed as an Azure App Service.
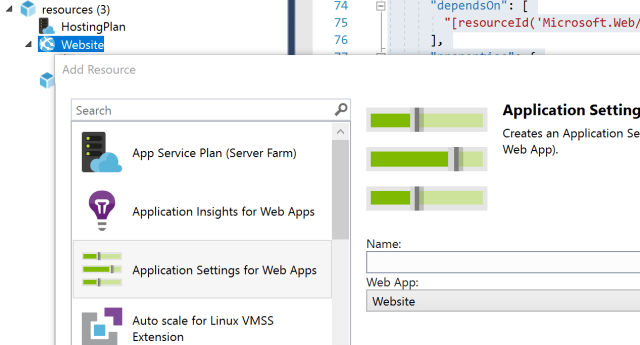
Add some Application settings to the WebSite. You can right click the Website blade in the Json Outline window.
You can validate the template using the Azure CLI. You can also deploy this to Azure using Visual Studio (Right click the project). Deploy this to the same Resource Group as the Key Vault which you have already created, or need to create.
Microsoft Documentation for Visual Studio
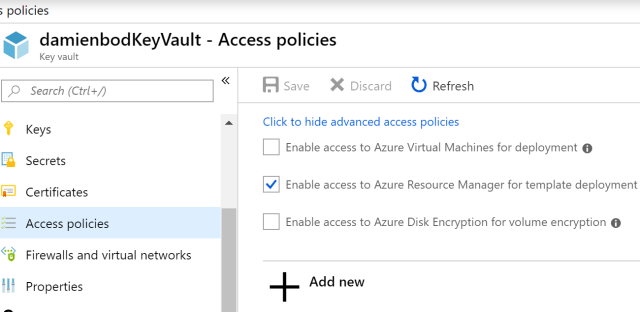
Configure the Key Vault for the template
Before the Key Vault can be used in an Azure ARM template, this needs to be activated in the Key Vault. Open the Key Vault in Azure, select the Access Policies blade, then Click to show advanced access policies. Set the Enable access to Azure Resource Manager for template deployment.
Using a Key Vault secret in the ARM template
The ARM template can now use the Azure Key Vault to set application settings. A parameter will be used for this. In the properties where the application settings are defined, add a new parameter which will be used for the Key Vault value. The name of the parameter is internal to the ARM template. In the following example, the app setting ClientSecret uses the ARM template parameter ‘name_of_parameter_in_template’
"resources": [
{
"name": "appsettings",
"type": "config",
"apiVersion": "2015-08-01",
"dependsOn": [
"[resourceId('Microsoft.Web/sites', variables('webSiteName'))]"
],
"tags": {
"displayName": "app"
},
"properties": {
"ClientSecret": "[parameters('name_of_parameter_in_template')]",
"ConnectionStrings:RedisCacheConnection": "[parameters('redisCacheConnection')]"
"AuthConfiguration:StsServerIdentityUrl": "https//localhost:44318",
}
}]
This is the code which matters:
[parameters('name_of_parameter_in_template')]
Add the parameter as a securestring in the template. You can navigate to this by using the Json Outline window in Visual Studio. The parameter used above, needs to be defined here, ie: ‘name_of_parameter_in_template’
"parameters": {
"name_of parameter_in_template": {
"type": "securestring"
},
In the WebSite.parameters.json file, add the Key Vault configuration. Use the parameter defined above, ‘name_of_parameter_in_template’ and add the Azure Key Vault using the reference json object. This object has two properties, a keyVault which requires the id, and the name of the secret.
Open the Azure Key Vault and click the Properties blade. The RESOURCE ID is the id which is required here. The secretName is the name of the secret in the secrets blade, which will be used.
"name_of_parameter_in_template": {
"reference": {
"keyVault": {
"id": "/subscriptions/..."
},
"secretName": "SecretMvcHybridBackChannel2"
}
},
When the ARM template is deployed, the application setting will use the Key Vault secret to get the value, and deploy this as an application setting in the Azure App Service. The application can then use the application setting. You need to deploy the ASP.NET Core application to the newly created Azure App Service.
Links
https://docs.microsoft.com/en-us/azure/azure-resource-manager/
https://docs.microsoft.com/en-us/azure/virtual-machines/azure-cli-arm-commands
https://docs.microsoft.com/en-us/azure/key-vault/key-vault-developers-guide
Using the Azure Key Vault to keep secrets out of your web app’s source code
https://stackoverflow.com/questions/40025598/azure-key-vault-access-denied
https://cmatskas.com/securing-asp-net-core-application-settings-using-azure-key-vault/
https://github.com/jayendranarumugam/DemoSecrets/tree/master/DemoSecrets
https://docs.microsoft.com/en-us/cli/azure/install-azure-cli-windows?view=azure-cli-latest
https://docs.microsoft.com/en-us/azure/key-vault/key-vault-developers-guide
Using the Azure Key Vault to keep secrets out of your web app’s source code
https://stackoverflow.com/questions/40025598/azure-key-vault-access-denied
https://cmatskas.com/securing-asp-net-core-application-settings-using-azure-key-vault/
https://github.com/jayendranarumugam/DemoSecrets/tree/master/DemoSecrets
https://docs.microsoft.com/en-us/cli/azure/install-azure-cli-windows?view=azure-cli-latest

[…] Deploying ASP.NET Core App Services using Azure Key Vault and Azure Resource Manager templates (Damien Bowden) […]