Tag Archives: OIDC
Add application security to the swiyu generic management verifier APIs using OAuth
The article looks at implementing security using OAuth for the swiyu Public Beta Trust Infrastructure generic containers. The container provides endpoint for OpenID verification and the management APIs. The OpenID endpoints are publicly accessible using a reverse proxy, the management APIs can only be accessed in the network and using an access token for app […]
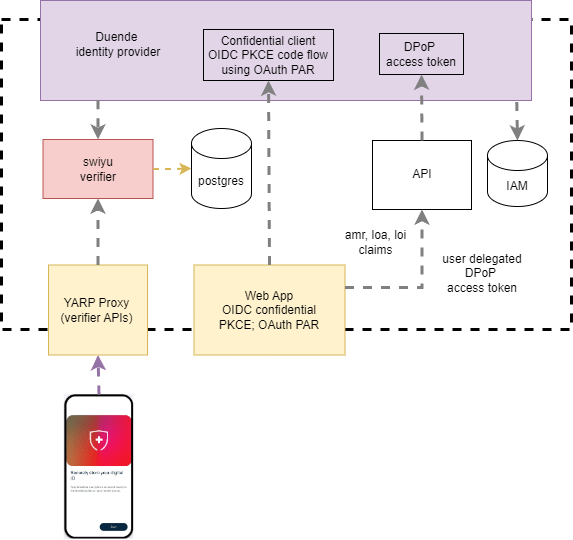
Isolate the swiyu Public Beta management APIs using YARP
This post looks at hardening the security for the swiyu public beta infrastructure. The generic containers provide both management APIs and wallet APIs which support the OpenID for Verifiable Presentations 1.0 specification. The management APIs require both network protection and application security. This post looks at implementing the network isolation. Code: https://github.com/swiss-ssi-group/swiyu-passkeys-idp-loi-loa Blogs in this […]
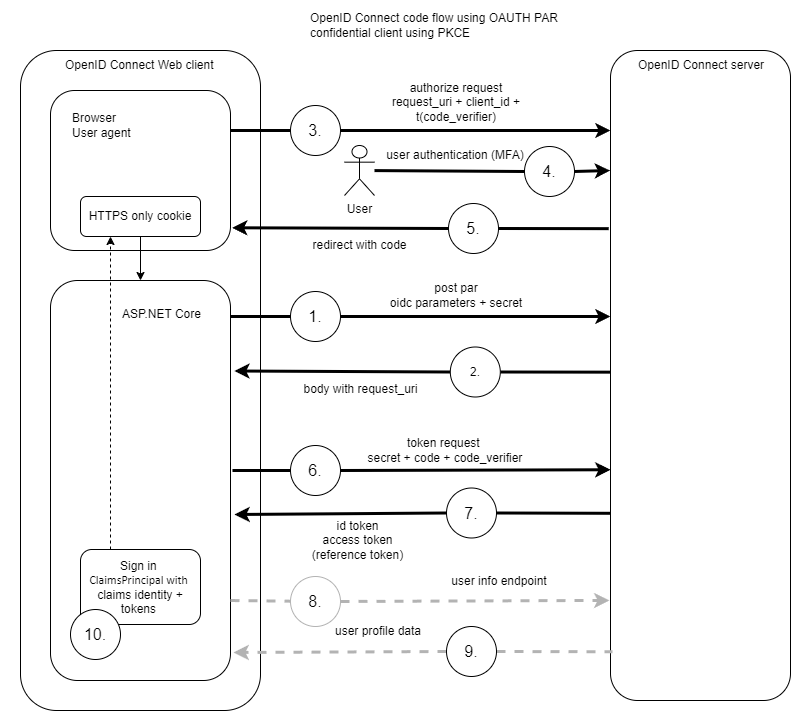
Use client assertions in ASP.NET Core using OpenID Connect, OAuth DPoP and OAuth PAR
This post looks at implement client assertions in an ASP.NET Core application OpenID Connect client using OAuth Demonstrating Proof of Possession (DPoP) and OAuth Pushed Authorization Requests (PAR). Code: https://github.com/swiss-ssi-group/swiyu-passkeys-idp-loi-loa Blogs in this series: Setup An ASP.NET code application is setup to authentication using OpenID Connect and OAuth PAR. The web application is an OIDC […]
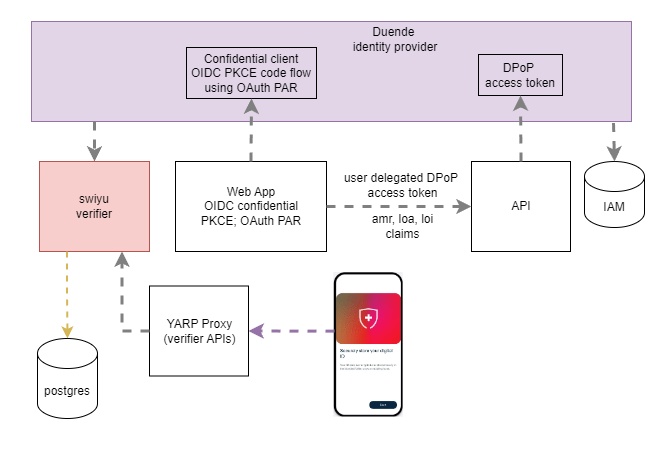
Implementing Level of Identification (LoI) with ASP.NET Core Identity and Duende
This article explores how to implement Level of Identification (LOI) in an ASP.NET Core application. The solution uses Duende IdentityServer as the OpenID Connect provider and ASP.NET Core Identity for user management. Identity verification is performed using the Swiyu Public Beta infrastructure. Any OpenID Connect client can consume the loi claim together with the loa […]
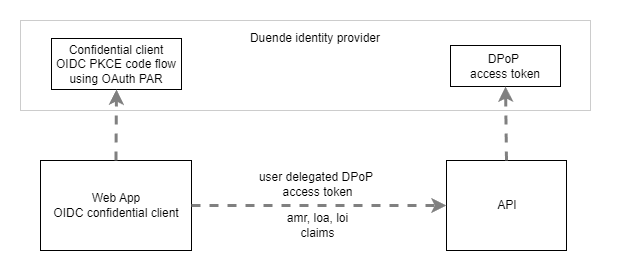
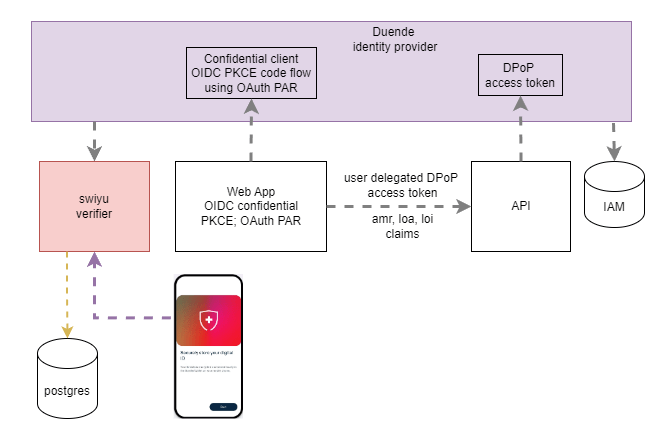
Implementing Level of Authentication (LoA) with ASP.NET Core Identity and Duende
This post shows how to implement an application which requires a user to authenticate using passkeys. The identity provider returns three claims to prove the authentication level (loa), the identity level, (loi) and the amr claim showing the used authentication method. Code: https://github.com/swiss-ssi-group/swiyu-passkeys-idp-loi-loa Blogs in this series: The amr claim and the loa claim returns […]

Implement forgot your password using swiyu, ASP.NET Core Identity and Aspire
This post show to implement a “Forgot your password” flow using the Swiss Digital identity and trust infrastructure, (swiyu) in an ASP.NET Core web application using ASP.NET Core Identity and Duende IdentityServer. The generic containers from swiyu are used to integrate the Swiss E-ID and the OpenID for Verifiable Presentations standards. .NET Aspire is used […]

Implement a secure MCP server using OAuth and Entra ID
The article shows how to implement a secure model context protocol (MCP) server using OAuth and Entra ID. The MCP server is implemented using ASP.NET Core and uses Microsoft Entra ID to secure the API. An ASP.NET Core application using Azure OpenAI and semantic kernel is used to implement the MCP client for the agent […]
Use EdDSA signatures to validate tokens in ASP.NET Core using OpenID Connect
Some identity providers use the EdDSA / ED25519 algorithm to sign and issue tokens. This post shows how to validate the tokens using the Nuget package from ScottBrady and ASP.NET Core. Using the default OpenID Connect setup, the keys are not read and the tokens cannot be validated. The error message could return something like […]

Implement ASP.NET Core OpenID Connect with Keycloak to implement Level of Authentication (LoA) requirements
This post looks at implementing an OpenID Connect client in ASP.NET Core and require a level of authentication (LoA) implemented using Keycloak. The applications are hosted using Aspire. The LoA is requested in Keycloak using the acr_values claim. Code: https://github.com/damienbod/IdentityExternalErrorHandling Setup The applications are implemented using Aspire. An ASP.NET Core application uses an OpenID Connect […]

Experimental alternative flow for OAuth First-Party Applications
This post looks at an alternative way of implementing a native app authentication and authorization. At present, a web browser is used to implement authentication of native applications when using OAuth and OpenID Connect. The alternative approach implemented in the post is based on the OAuth 2.0 for First-Party Applications draft and adapted to be […]
