Tag Archives: Authorization
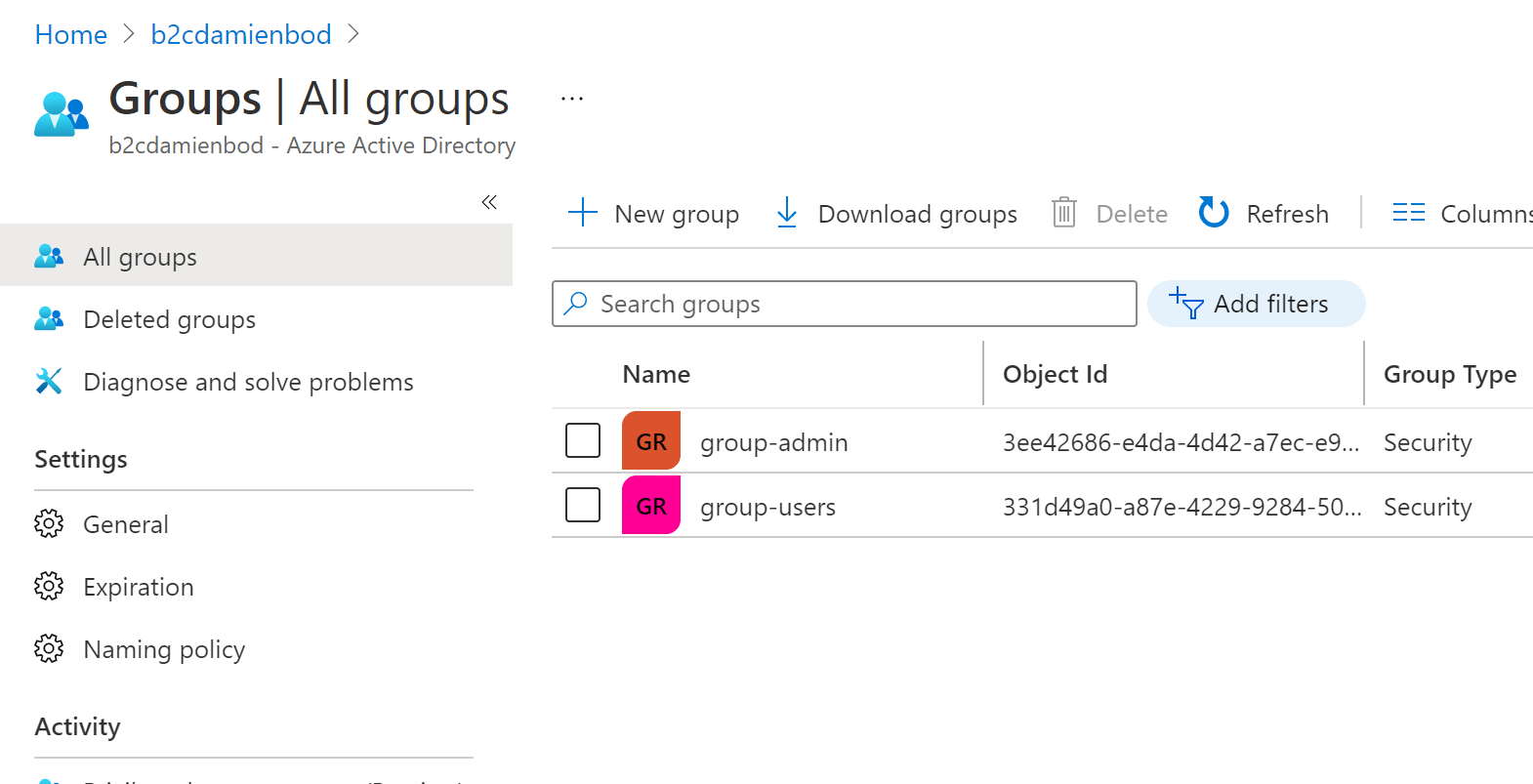
ASP.NET Core authorization using Entra External ID CIAM and Azure AD security groups
This article looks at implementing authorization in Microsoft Entra External ID for customers (CIAM) using Azure AD delegated roles. The roles can be assigned to users or groups in an Azure Enterprise application. Code: https://github.com/damienbod/EntraExternalIdCiam Blogs in this series In Azure AD it has been possible to use roles with users and groups to implement […]

Implementing authorization in Blazor ASP.NET Core applications using Azure AD security groups
This article shows how to implement authorization in an ASP.NET Core Blazor application using Azure AD security groups as the data source for the authorization definitions. Policies and claims are used in the application which decouples the descriptions from the Azure AD security groups and the application specific authorization requirements. With this setup, it is […]
Using Azure security groups in ASP.NET Core with an Azure B2C Identity Provider
This article shows how to implement authorization in an ASP.NET Core application which uses Azure security groups for the user definitions and Azure B2C to authenticate. Microsoft Graph API is used to access the Azure group definitions for the signed in user. The client credentials flow is used to authorize the Graph API client with […]
Using Azure AD groups authorization in ASP.NET Core for an Azure Blob Storage
This post show how Azure AD groups could be used to implement authorization for an Azure Blob storage and used in an ASP.NET Core Razor page application to authorize the identities. The groups are assigned the roles in the Azure Storage. Azure AD users are added to the Azure AD groups and inherit the group […]
Adding ASP.NET Core authorization for an Azure Blob Storage and Azure AD users using role assignments
This post shows how authorization can be implemented for Azure Storage Blob containers in an ASP.NET Core web application. The two roles Storage Blob Data Contributor and Storage Blob Data Reader are used to authorize the Azure AD users which use the Blob storage container. Users are assigned the roles using role assignment. This authorization […]
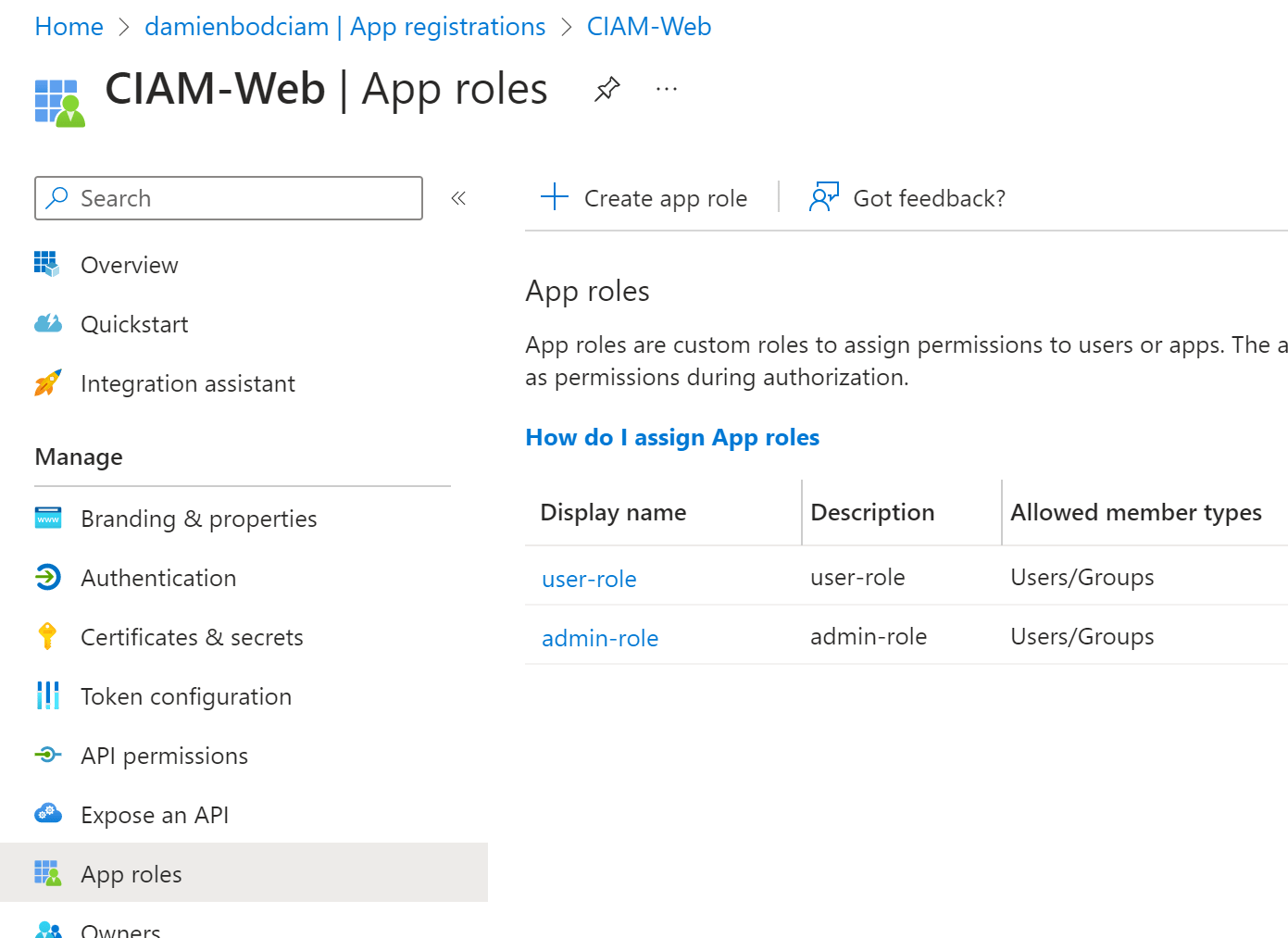
Implement app roles authorization with Azure AD and ASP.NET Core
This post shows how to implement Azure AD App roles and applied to users or groups in Azure AD. The roles are used in an ASP.NET Core Razor page application as well as a ASP.NET Core API. The roles from the access token and the id token are used to authorize the identity which is […]
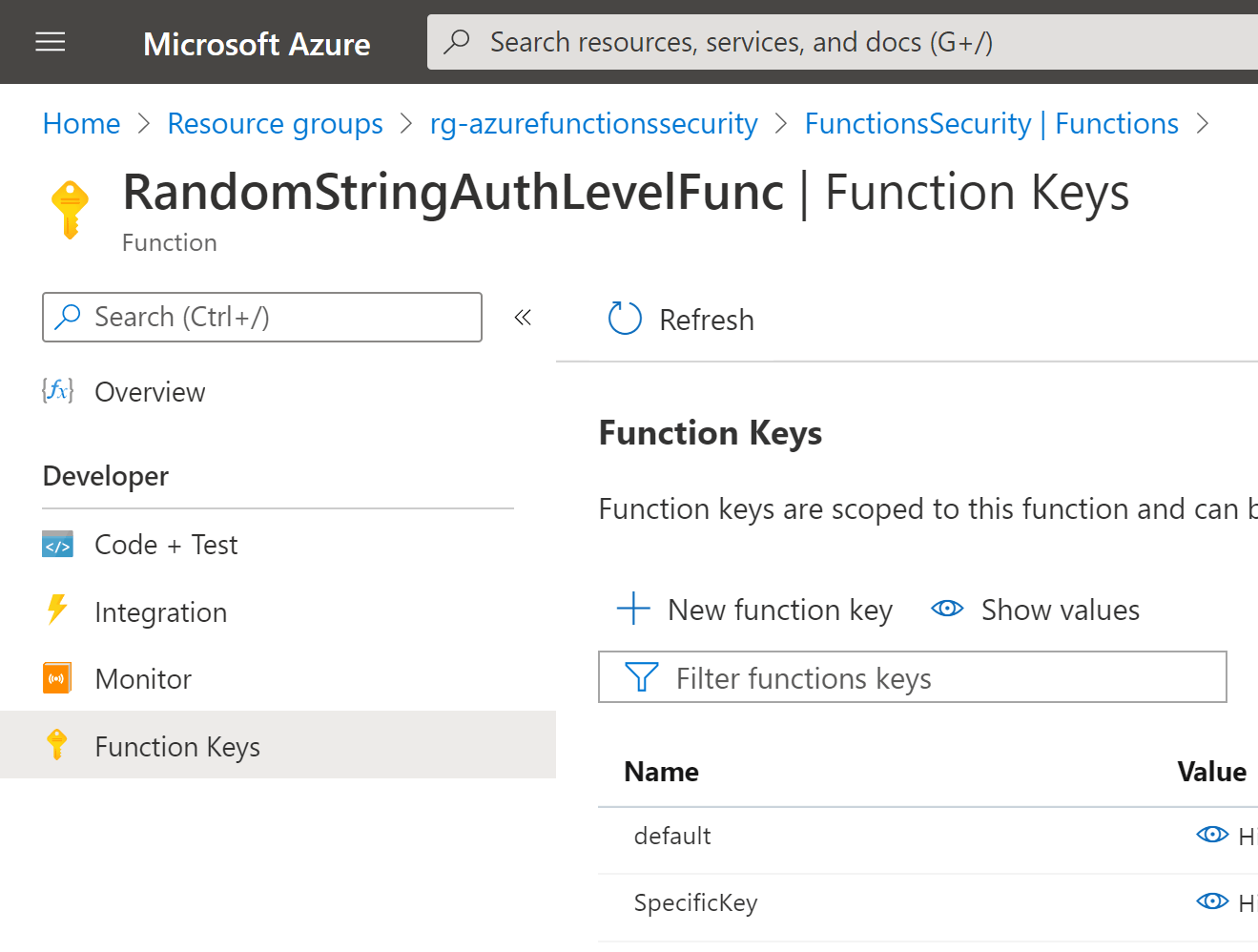
Securing Azure Functions using API Keys
This article shows how to secure Azure Functions using API Keys. This is useful, if you have no control over the API client implementation, the client code base cannot be easily changed or the client is not Azure hosted. This should only be used with trusted clients and is for machine to machine usage. Code: […]
Requiring MFA for Admin Pages in an ASP.NET Core Identity application
This article shows how MFA could be forced on users to access sensitive pages within an ASP.NET Core Identity application. This could be useful for applications where different levels of access exist for the different identities. For example, users might be able to view the profile data using a password login, but an administrator would […]
Using HTTP Request Routes, Request Body, and Query string parameters for Authorization in ASP.NET Core
This post shows how HTTP route parameters, a HTTP request body or HTTP request query string parameters can be used for authorization in ASP.NET Core. Code: https://github.com/damienbod/AspNetCoreWindowsAuth Authorization using ASP.NET Core Route parameters An AuthorizationHandler can be used to implement authorization logic in ASP.NET Core. The handler can authorize HTTP requests using a route parameter […]

Securing an ASP.NET Core Razor Page App using OpenID Connect Code flow with PKCE
This article shows how to secure an ASP.NET Core Razor Page application using the Open ID Connect code flow with PKCE (Proof Key for Code Exchange). The secure token server is implemented using Duende IdentityServer but any secure token server (STS) can be used which supports PKCE. Code: https://github.com/damienbod/AspNetCoreHybridFlowWithApi See WebCodeFlowPkceClient project. History An ASP.NET […]
