In Azure AD, a client application with no user (daemon client) which uses an access token to access an API protected with Microsoft Identity needs to use an Azure API Registration with App Roles. Scopes are used for delegated flows (with a User and a UI login). This is Azure AD specific not OAuth2. This post shows the portal steps to setup an Azure App Registration with Azure App roles.
Code: https://github.com/damienbod/GrpcAzureAppServiceAppAuth
This is a follow up post to this article:
To set this up, an Azure App Registration needs to be created. We would like to allow only single tenant Azure AD access. This is not really used as the client credentials configuration with a secret or a certificate. No platform needs to be selected as this is only an API.

In the App Registration Expose an API blade, the Application ID URI must be set.

Now create an App role for the application. Set the Allow member types to Applications. This is added to the claims in the access token.

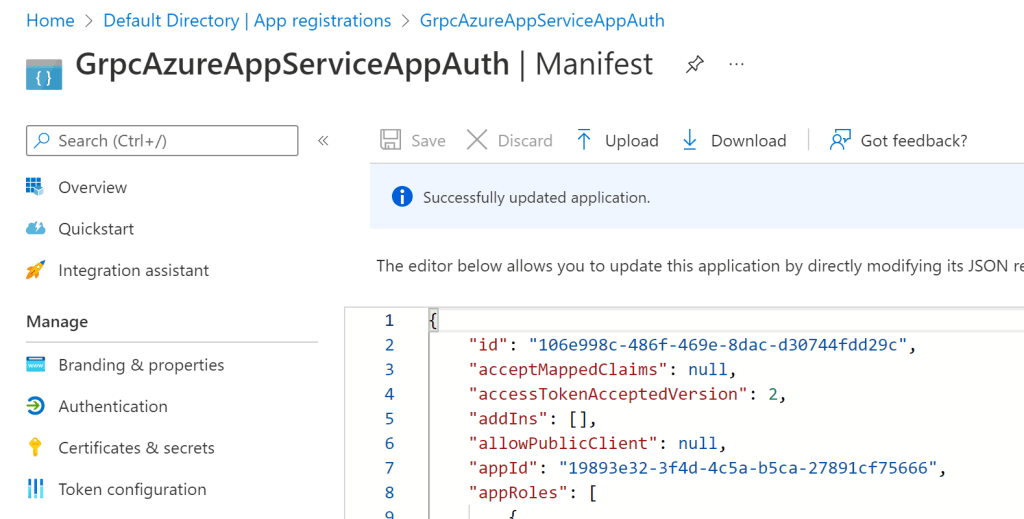
In the Manifest, set the accessTokenAcceptedVersion to 2 and save the manifest.
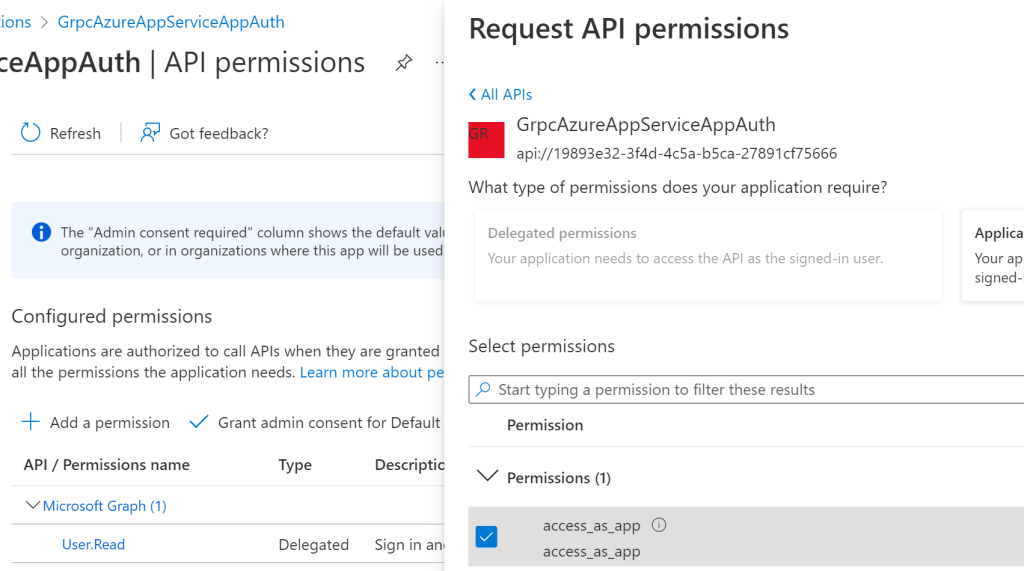
Now the App Registration needs to allow the App role. In the API permissions blade, search for the name of the Azure App Registration in the APIs tab and select the new App Role you created as a allowed permission. You must then grant admin consent for this.
You need to use a secret or a certificate to acquire the access token. This needs to be added to the Azure App Registration. Some type of rotation needs to be implemented for this.
You can validate the app role in the access token claims. If the roles claim is not included in the access token, the API will return a 401 to the client without a good log message.
Next steps would be to automate this using Powershell or Terreform and to solve the secret, certification rotation.
Links:
https://docs.microsoft.com/en-us/azure/active-directory/develop/scenario-daemon-overview
https://github.com/Azure-Samples/active-directory-dotnetcore-daemon-v2/tree/master/2-Call-OwnApi

[…] Setup application client in Azure App Registration with App roles to use a web API (Damien Bowden) […]
[…] Setup application client in Azure App Registration with App roles to use a web API – Damien Bowden […]