This article uses the the ASP.NET Core 2.1 MVC template and shows how to secure the CDN links using the integrity parameter.
A new ASP.NET Core MVC application was created using the 2.1 template in Visual Studio.

This template uses HTTPS per default and has added some of the required HTTPS headers like HSTS which is required for any application. The template has added the integrity parameter to the javascript CDN links, but on the CSS CDN links, it is missing.
<script src="https://ajax.aspnetcdn.com/ajax/jquery/jquery-2.2.0.min.js" asp-fallback-src="~/lib/jquery/dist/jquery.min.js" asp-fallback-test="window.jQuery" crossorigin="anonymous" integrity="sha384-K+ctZQ+LL8q6tP7I94W+qzQsfRV2a+AfHIi9k8z8l9ggpc8X+Ytst4yBo/hH+8Fk"> </script>
If the value of the integrity is changed, or the CDN script was changed, or for example a bitcoin miner was added to it, the MVC application will not load the script.
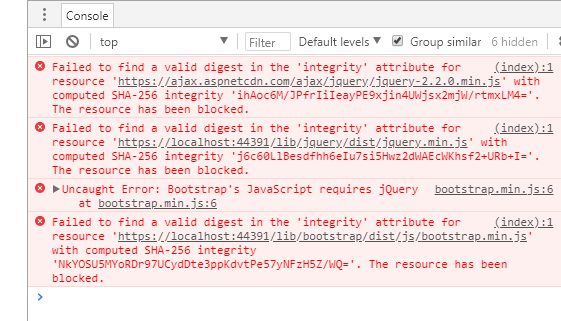
To test this, you can change the value of the integrity parameter on the script, and in the production environment, the script will not load and fallback to the localhost deployed script. By changing the value of the integrity parameter, it simulates a changed script on the CDN. The following snapshot shows an example of the possible errors sent to the browser:
Adding the integrity parameter to the CSS link
The template creates a bootstrap link in the _Layout.cshtml as follows:
<link rel="stylesheet" href="https://ajax.aspnetcdn.com/ajax/bootstrap/3.3.7/css/bootstrap.min.css"
asp-fallback-href="~/lib/bootstrap/dist/css/bootstrap.min.css"
asp-fallback-test-class="sr-only" asp-fallback-test-property="position" asp-fallback-test-value="absolute" />
This is missing the integrity parameter. To fix this, the integrity parameter can be added to the link.
<link rel="stylesheet"
integrity="sha384-BVYiiSIFeK1dGmJRAkycuHAHRg32OmUcww7on3RYdg4Va+PmSTsz/K68vbdEjh4u"
crossorigin="anonymous"
href="https://ajax.aspnetcdn.com/ajax/bootstrap/3.3.7/css/bootstrap.min.css"
asp-fallback-href="~/lib/bootstrap/dist/css/bootstrap.min.css"
asp-fallback-test-class="sr-only"
asp-fallback-test-property="position"
asp-fallback-test-value="absolute" />
The value of the integrity parameter was created using SRI Hash Generator. When creating this, you have to be sure, that the link is safe. By using this CDN, your application trusts the CDN links.

Now if the css file was changed on the CDN server, the application will not load it.
The CSP Header of the application can also be improved. The application should only load from the required CDNs and no where else. This can be forced by adding the following CSP configuration:
content-security-policy: script-src 'self' https://ajax.aspnetcdn.com; style-src 'self' https://ajax.aspnetcdn.com; img-src 'self'; font-src 'self' https://ajax.aspnetcdn.com; form-action 'self'; frame-ancestors 'self'; block-all-mixed-content
Or you can use NWebSec and add it to the startup.cs
app.UseCsp(opts => opts
.BlockAllMixedContent()
.FontSources(s => s.Self()
.CustomSources("https://ajax.aspnetcdn.com"))
.FormActions(s => s.Self())
.FrameAncestors(s => s.Self())
.ImageSources(s => s.Self())
.StyleSources(s => s.Self()
.CustomSources("https://ajax.aspnetcdn.com"))
.ScriptSources(s => s.Self()
.UnsafeInline()
.CustomSources("https://ajax.aspnetcdn.com"))
);
Links:
https://developer.mozilla.org/en-US/docs/Web/Security/Subresource_Integrity
https://www.troyhunt.com/protecting-your-embedded-content-with-subresource-integrity-sri/
https://scotthelme.co.uk/tag/cdn/
https://rehansaeed.com/tag/subresource-integrity-sri/
https://rehansaeed.com/subresource-integrity-taghelper-using-asp-net-core/

[…] Securing the CDN links in the ASP.NET Core 2.1 templates – Damien Bowden […]
I wrote an ASP.NET Core tag helper to make this much easier:
https://rehansaeed.com/tag/subresource-integrity-sri/
Hi Muhammad
Thanks for the link, looks cool
Greetins Damien
[…] Securing the CDN links in the ASP.NET Core 2.1 templates: https://damienbod.com/2018/03/14/securing-the-cdn-links-in-the-asp-net-core-2-1-templates/ […]
[…] Securing the CDN links in the ASP.NET Core 2.1 templates: https://damienbod.com/2018/03/14/securing-the-cdn-links-in-the-asp-net-core-2-1-templates/ […]